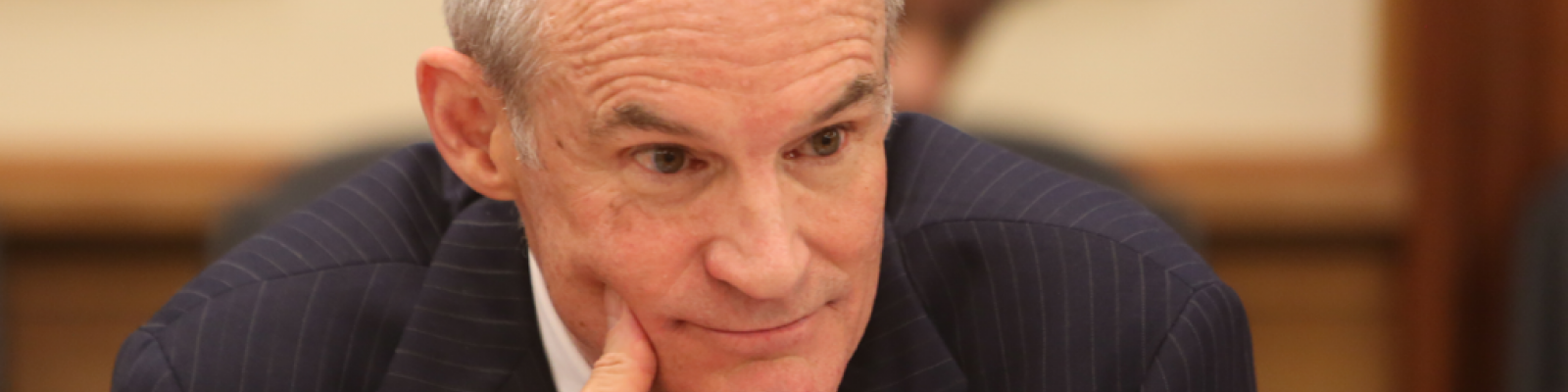
Bruce McConnell Interviewed by The Open Group
Senior Vice President at EWI, Bruce McConnell speaks with The Open Group about global cooperation and cybersecurity for governments and businesses.
In your role as Deputy Under Secretary for Cybersecurity in the Obama Administration, you were responsible for protecting U.S. infrastructure from cyber threats. In your estimation, what are the most serious threats in cyberspace today?
User error. I say that because a lot of people these days like to talk about these really scary sounding cyber threats, like some nation state or terrorist group that is going to take down the grid or turn off Wall Street, and I think we spend too much time focusing on the threat and less time focusing on other aspects of the risk equation.
The three elements of risk are threats, vulnerability and consequences. A lot of what needs to be done is to reduce vulnerability. Part of what EWI is working on is promoting the availability of more secure information and communications in technology so that buyers and users can start with an infrastructure that is actually defensible as opposed to the infrastructure we have today which is very difficult to defend. We figure that, yes, there are threats, and yes, there are potential consequences, but one of the places that we need more work in particular is reducing vulnerabilities.
EWI is also working on reducing threats and consequences by working with countries to, for example, agree that certain key assets, such as core Internet infrastructure or financial services markets and clearinghouses should not be attacked by anybody. You have to work all aspects of the equation.
What steps can be taken by governments or businesses to better shore up the infrastructure from cyber threats?
One of the things that has been missing is a signal from the marketplace that it wants more secure technology. There’s been complacency for a long time and denial that this is really a problem, and the increasing visibility of these high profile attacks, like on Target, Sony, JP Morgan Chase and others, are getting companies at the most senior level—in the C-Suite and in the Boardroom—to start paying attention and asking questions of their IT team: ‘How are we protecting ourselves?’ ‘Are we going to be the next ones?’ Because there are two kinds of companies in the U.S.—those that have been hacked and those that know they’ve been hacked.
One of the things EWI has been working on with The Open Group and some of the large IT companies is a set of questions that buyers of IT could ask suppliers about what they do to make sure their products are secure—how they are paying attention to their supply chain, who’s responsible for security at their organization, etc. We think that companies and the government—from the standpoint of education, not regulation—can do more to send signals to the marketplace and suppliers so that they offer more secure technology. In the past customers haven’t been willing to pay more for security—it does cost more. I think that’s changing, but we need to give them tools to be able to ask that question in a smart way.
With respect to government specifically, I think one of the great things the U.S government has done recently is coming out with a Cybersecurity Framework, which was developed mostly by the private sector. NIST, of course, acted as the facilitator, but there’s a lot of uptake there that we’re seeing in terms of companies and sectors—like the financial services sector—adopting and adapting it. It has raised the level of security inside corporations. Insurance carriers are starting to use it as the basis for underwriting insurance policies. It’s not mandatory but it’s a good guidepost, and I think it will become a standard of care.
Why has there been that level of complacency for so long?
I think it’s two things, and they’re both cultural.
One is that the IT community inside companies has not been able to communicate effectively to senior management regarding the nature of the threat or the degree of risk. They don’t speak the same language. When the CFO comes into the CEO’s office and talks about foreign exchange exposure or the General Counsel comes in and speaks about reputational risk, they’re speaking a language that most CEOs can understand. But when the IT guy comes in and talks about Trojans and botnets, he’s speaking a foreign language. There’s been a tendency for that message to not be expressed in business terms that the CEO can understand or be able to quantify and think about as a risk. But it’s a risk just like any of those other risks—foreign exchange risk, competitive risk, natural disasters, cyber attacks. I think that’s changing now, and some companies are pulling the Chief Information Security Officer out from under the CIO and having them report to the Chief Risk Officer, whether it’s the General Counsel or the CFO. That puts them in a different position, and then it can be positioned against other risks and managed in a different way. It’s not a technology problem, it’s as much a human problem—it’s about training employees, it’s about background checks on systems administrators.
The second piece is that it’s invisible. Unlike a hurricane or fire, where you can see the damage, the damage from a cyber attack is invisible. When I was at Homeland Security, we said, ‘What’s it going to take for people to wake up? Well, something really bad will have to happen.’ And something really bad is happening all the time. There’s billions of dollars of financial fraud and theft, there’s theft of intellectual property, the theft of identities—there’s lots of bad things happening but they’re kind of invisible. People don’t react to something they can’t see, we react to the threats that we can see. I think that there’s just a conceptual gap that security professionals haven’t figured out how to convert into something tangible.
How much difference is there anymore in the threats that governments are facing as opposed to businesses? Are these things converging more?
We certainly saw the Office of Personnel Management got the same kind of breaches that Target got: people’s personal data. In the intellectual property area, attackers steal from both businesses and governments. Fraud is probably more directed at businesses and banks just because they handle the money, although some of the IRS data will probably be used to perpetrate fraud. Certainly the government has some systems that are of higher value to society than any single corporate system, but if the core Internet infrastructure, which is owned and run by companies, went down, that would be bad for everybody.
I think the threats are converging also in the sense that attackers are always looking for high-value targets so both governments and companies these days have high-value targets. And they use similar tactics—what we saw was that one family of malware would be used to attack government systems and a slightly different version of that family would be used to attack commercial systems. It was the same kind of malware, and maybe the same perpetrators.
Your session at The Open Group Baltimore event is focused on global cooperation in cyberspace. Where does global cooperation in cyberspace stand today, and why is it important to have that cooperation?
It’s in the spirit of the Baltimore event—Boundaryless Information Flow™. The Internet is a global phenomenon and not a great respecter of national boundaries. The information and technology we all use comes from all over the world. From a security and management standpoint, this is not something that any single government can manage on its own. In order to allow for the boundaryless movement of information in a secure way, governments have to work together to put the right policies and incentives in place. That includes cooperating on catching and investigating cyber criminals. It involves the matter of ensuring buyers can get the best, most secure technology no matter where it is manufactured. It involves cooperating on the types of behavior that are unacceptable in cyberspace. Even reaching agreement on what institutions can be used to manage this global resource is crucial because there’s no real governance of the Internet—it’s still run on an ad hoc basis. That’s been great, but the Internet is becoming too important to be left to everybody’s good will. I’ll cover these issues in more depth in Baltimore.
Who is working on these issues right now and what kind of things are they doing? Who are the “allies” in trying to put together global cooperation initiatives?
There are a lot of different coalitions of people working together. They range from a group called the United Nations Group of Governmental Experts, which by the time of the Baltimore conference will have conducted its fourth in a series of meetings over a two-year period to discuss norms of behavior in cyberspace, along the lines of what kinds of behaviors should nation states not engage in vis a vis cyberattacks. There’s a case where you have a U.N.-based organization and 20 countries or so working together to try to come up with some agreements in that area. Certainly EWI’s work is supported primarily by companies, both U.S. and foreign companies. We bring a broad multi-stakeholder group of people together from countries, companies and non-profit organizations from all the major cyber powers, whether they are national cyber powers like China, Russia, U.S, Germany, India, or corporate cyber powers like Microsoft and Huawei Technologies because in the Internet, companies are important. There are a lot of different activities going on to find ways of cooperating and increasingly recognize the seriousness of the problem.
In terms of better cooperation, what are some of the issues that need to be addressed first and how can those things be better accomplished?
There are so many things to work on. Despite efforts, the state of cooperation isn’t great. There’s a lot of rhetoric being applied and countries are leveling charges and accusing each other of attacking them. Whether or not those charges are true, this is not the way to build trust and cooperation. One of the first things that governments really need to do if they want to cooperate with each other is tone down the rhetoric. They need to sit down, listen to each other and try to understand where the other one’s coming from rather than just trading charges in public. That’s the first thing.
There’s also a reflection of the lack of trust between the major cyber powers these days. How do you build trust? You build trust by working together on easy projects first, and then working your way up to more difficult topics. EWI has been promoting conversations between governments about how to respond if there’s a server in one country that’s been captured by a bot and is attacking machines in another country. You have to say, ‘Could you take a look at that?’ But what are the procedures for reducing the impact of an incident in one country caused by malware coming from a server in of another country? This assumes, of course, that the country itself is not doing it deliberately. In a lot of these attacks people are spoofing servers so it looks like they’re coming from one place but it’s actually originating someplace else. Maybe if we can get governments cooperating on mutual assistance in incident response, it would help build confidence and trust that we could work on larger issues.
As the Internet becomes increasingly more crucial to businesses and government and there are more attacks out there, will this necessitate a position or department that needs to be a bridge between state departments and technology? Do you envision a role for someone to be a negotiator in that area and is that a diplomatic or technological position or both?
Most of the major national powers have cyber ambassadors. The German’s Foreign Office has a cyber ambassador, the Chinese have one. The U.S. has a cyber coordinator, the French have a cyber ambassador and the British just named a new cyber ambassador. States are recognizing there is a role for the foreign ministry to play in this area. It’s not just a diplomatic conversation.
There are also global forums where countries, companies and NGOs get together to talk about these things. EWI hosts one every year – this year’ it’s in New York September 9-10. I think there are a lot of places where the conversations are happening. That gets to a different question: At some point do we need more structure in the way these issues are managed on a global basis? There’s a big debate right now just on the topic of the assignment of Internet names and numbers as the U.S. lets go of its contract with ICANN—who’s going to take that on, what’s it going to look like? Is it going to be a multi-stakeholder body that involves companies sitting at the table or is it only going to be only governments?
Do you see a role for technology standards in helping to foster better cooperation in cyberspace? What role can they play?
Absolutely. In the work we’re doing to try to tell companies they want more secure products. We’re referencing a lot of different standards including those The Open Group and the Trusted Technology Forum have been developing. Those kind of technical standards are critical to getting everyone on a level playing fields in terms of being able to measure how secure products are and to having a conversation that’s fact-based instead of brochure based. There’s a lot of work to be done, but they’re going to be critical to the implementation of any of these larger cooperative agreements. There’s a lot of exciting work going on.
Click here to read the interview on The Open Group website