The Objective
The objective of the Global Cooperation in Cyberspace program is to reduce conflict, crime and other disruptions in cyberspace and promote stability, innovation and inclusion.
The Challenge
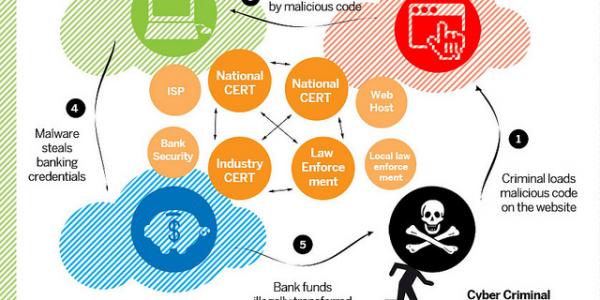
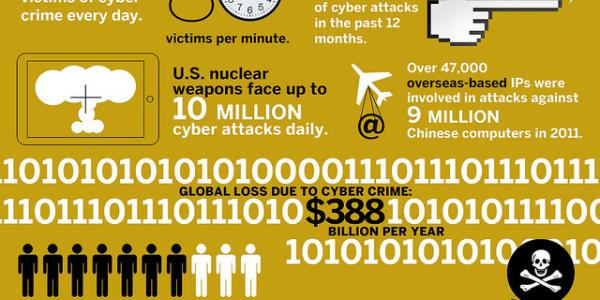
Cyber is at the nexus of the greatest security threats the world faces. The innovation that creates so many efficiencies and connections is also a source of risk. Unproven technology contains vulnerabilities that malicious actors exploit. Roles and capabilities for maintaining security and protecting freedom are muddied. The structure of the global economy is shifting on its axis. Social media connects us with our loved ones and provides platforms for disruptive disinformation. Cyber weapons destabilize longstanding international security arrangements. The divide among digital haves and have-nots remains significant; billions of users are expected to connect to cyberspace over the next several years, creating new opportunities as well as societal vulnerabilities and risk, particularly in the Global South.
The Opportunity
Global cooperation is essential to successfully address existing and emerging conflicts—both in cyberspace and across all areas of human endeavor. To this end, the EastWest Institute began its cyber work in 2009 as the pioneer organization that initiated a global dialogue on cyberspace security, diplomacy and deterrence. Past successes have helped shorten repair times for damaged undersea cables, reduce spam on a global basis, promote balanced encryption policies, build bilateral confidence and trust between East and West to improve crisis response and combat malicious hackers, and develop norms of responsible behavior in cyberspace.
Working with government, business and civil society leaders from around the world, the program has highlighted three objectives to be pursued towards a safer and more secure Internet:
- Promote cybersecurity defenses to increase the costs and reduce the benefits cyber attackers can expect.
- Advocate for limits on the use of cyberspace and cyber tools for offensive purposes.
- Facilitate enhanced operational collaboration across borders and among adversaries.
The Process
The Global Cooperation in Cyberspace program utilizes the EastWest Institute’s proven trust building process—convene, reframe and mobilize:
1. Convene:
EWI convenes many meetings, including bilateral and trilateral country-to-country discussions, focused workshops on specific topics, and broader strategy development roundtables. In recent years, EWI has hosted sessions on the geopolitical and economic effects of cybersecurity at the Munich Security Conference; a workshop on protectionist government actions in the global ICT market; and a dialogue on trilateral cyberspace cooperation between China, India and the United States.
The EastWest Institute has also convened policymakers, business leaders, technical experts and civil society through its Global Cyberspace Cooperation Summits. The summits provide a crucial forum for building international, private-public actions to foster international cooperation in cyberspace and have taken place in Dallas, London, New Delhi, Silicon Valley, Berlin, New York and Berkeley. Each summit brought together between 200 and 400 leaders from more than 40 countries to craft solutions to threats facing our digital world.
2. Reframe:
In 2020, the program will continue to develop and advocate for recommended changes in national and corporate policies and procedures. The principal means of developing these recommendations is through the work of five collaborative breakthrough groups, composed of decision-makers from key sectors around the world:
- Increasing the Global Availability and Use of Secure ICT Products and Services
- Secure, Resilient Cities and the Internet of Things
- Systemic Risk and Cyber Insurance
- Promoting Norms of Responsible Behavior in Cyberspace
- Ubiquitous Encryption and Lawful Government Access
As recommendations mature, EWI leads the preparation of reports detailing and supporting the conclusions. The latest report, Weathering TechNationalism: A Security and Trustworthiness Framework to Manage Cyber Supply Chain Risk, was released in May 2020. The report provides a framework to overcome the trust gap between ICT buyers, vendors, and operators and their respective governments instead of relying on "TechNationalism”—measures that favor ICT products and services sold by companies headquartered domestically or in allied states—to improve overall ICT security.
Before that, Cyber Insurance and Systemic Market Risk was released in June 2019. This report provides an analytical framework to better understand and address the systemic nature of cyber risk and the challenges it presents to the growing cyber insurance market. The report emphasizes the role of the insurance industry, risk management firms and governments as drivers for robust cyber standards, resiliency, and security, through a set of proposed policy recommendations. In February 2019, the program published, Smart and Safe: Risk Reduction in Tomorrow’s Cities. This guide is geared toward city executives and policymakers, to raise awareness and offer recommendations on the key issues and challenges associated with deploying smart technologies and the Internet of Things in urban environments. In February 2018 at the Munich Security Conference, the program released Encryption Policy in Democratic Regimes: Finding Convergent Paths and Balanced Solutions. This report recommends ways to balance the legitimate needs of law enforcement with cybersecurity and privacy. In 2016 the program published Purchasing Secure ICT Products and Services: A Buyers Guide which offered a structure for conversations between ICT buyers and suppliers, enabling governments and organizations to manage the risks they face from cybersecurity vulnerabilities in the commercial products and services they use.
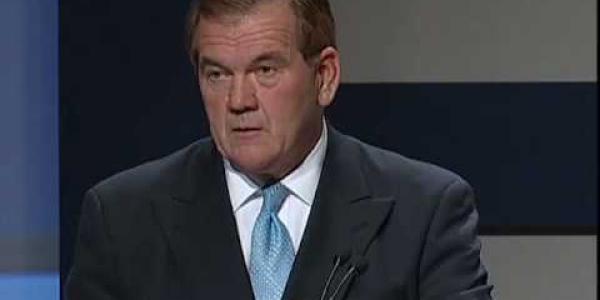
EWI also co-directs the Secretariat for the Global Commission on the Stability of Cyberspace (GCSC) alongside The Hague Centre for Strategic Studies. The Commission, which was launched at the 2017 Munich Security Conference, is a global body working to develop proposals for norms and policy initiatives to improve the stability and security of cyberspace. Co-chaired by Michael Chertoff, former U.S. Secretary of Homeland Security, and Latha Reddy, India’s former national security advisor, the 26 Commissioners bring governmental, industry, technical and civil society perspectives on cyberspace from north and south, east and west.
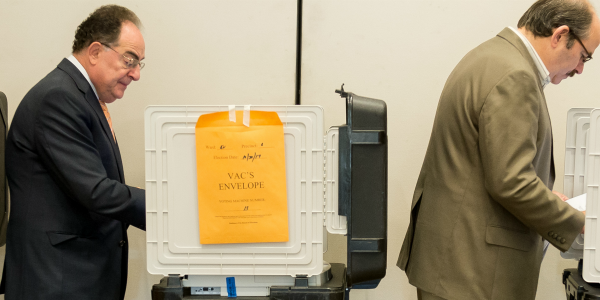
A non-governmental body, the GCSC complements other global initiatives such as the work of the United Nations Group of Governmental Experts. In 2017, the Commission released a “Call to Protect the Public Core of the Internet” and a "Call to Protect the Electoral Infrastructure." In 2018, the Commission released a Norm Package that contains six new norms including:
- Norm to Avoid Tampering
- Norm Against Commandeering of ICT Devices into Botnets
- Norm for States to Create a Vulnerability Equities Process
- Norm to Reduce and Mitigate Significant Vulnerabilities
- Norm on Basic Cyber Hygiene as Foundational Defense
- Norm Against Offensive Cyber Operations by Non-State Actors
In November 2019, the Global Commission on the Stability of Cyberspace issued its final report, Advancing Cyberstability, which represents the culmination of the Commission’s work over the last three years, offering a framework to advance cyberstability, a set of four principles, six recommendations, and eight norms that address critical elements of implementation, monitoring and accountability.
3. Mobilize:
The EastWest Institute mobilizes a global network of policymakers and specialists, all serving voluntarily, to advocate for policy breakthroughs. It will lead the mobilization for advocacy of the recommendations it develops—as well as those of its fellows and breakthrough groups—in capitals and corporate headquarters worldwide.
Supporters
The Global Cooperation in Cyberspace program thrives on the support and leadership provided by: