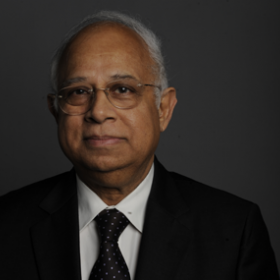
Stuxnet -- A Cyber "Cold Start"?
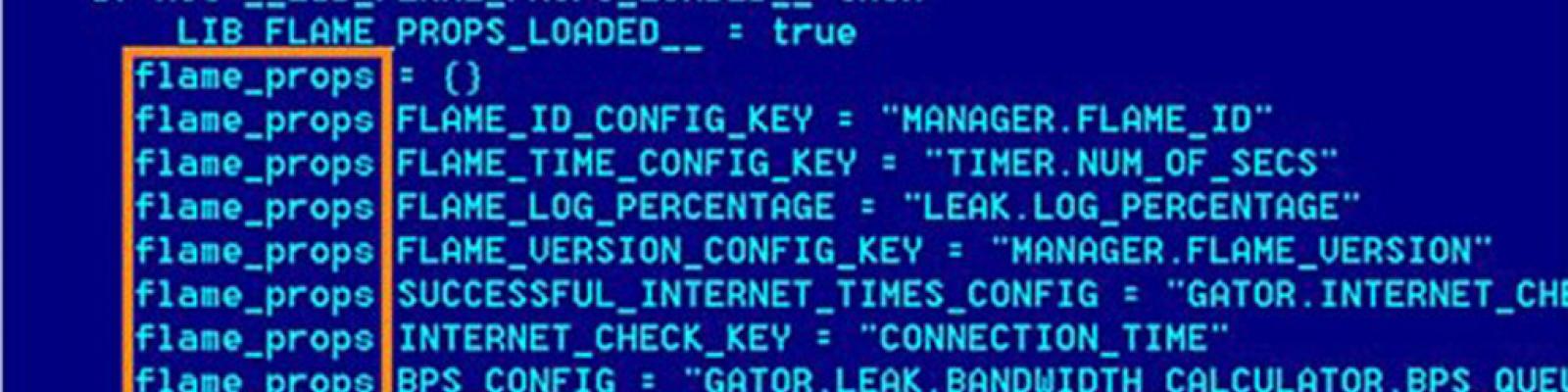
Writing for The News, EWI Director Ikram Sehgal discusses Stuxnet, the recent cyber attack on Iran’s nuclear power plant.Stuxnet is a “malware” that spies on and reprograms industrial systems – the first form of malware to successfully attack critical industrial infrastructure.
“Designed as a kind of guided missile to target facilities, this virus is not the work of some odd hacker sitting at a computer,” Sehgal explains. The complexity of the attack is such that it appears to be the work of a government or a government-level organization. Sehgal warns, “A virus of this type can effectively destroy an entire factory or power plant causing them to fail in ways virtually undetectable, the results could be as spectacular as the detonation of a bomb. There would be no trace of the bomber, or any way to find out who it is.”
Citing EWI’s 2010 Cybersecurity conference in Dallas and Lieutenant General (USAF Ret) Harry D. Raduege, Jr., Sehgal introduces Raduege’s concept of the “cyber triad.” The “cyber triad” is a play off the concept of the “strategic triad” from the Cold War. Sehgal writes that the strategic triad would be comprised of “resilience,” “attribution” and “offensive capabilities.” Resilience would help discourage an attack, while at the next level attribution would help identify the attacker, and finally, offensive capabilities would allow for a response to an attack.
“Our strategic planners must put in place (and soon) a potent and credible defense mechanism against of cyber ‘COLD START’ from malware of the Stuxnet-kind,” concludes Sehgal.